The modern digital landscape is built on a foundation of constant identification and data collection. Every time you navigate the web, websites silently gather a vast array of signals from your device, browser, and network environment. These data points are aggregated to create a unique “digital fingerprint” that allows platforms to track and recognize you with startling accuracy, even if you clear your cookies or use traditional privacy methods.
For online professionals, this pervasive tracking isn’t just a privacy concern—it’s a significant operational hurdle. Digital marketers, software testers, security researchers, and e-commerce entrepreneurs frequently need to interact with web platforms using multiple, independent identities. Without a way to ensure secure browsing through complete isolation, platforms can easily link these separate accounts together, leading to restrictions, bans, or compromised data.
Understanding the Role of an Anti-detect Browser
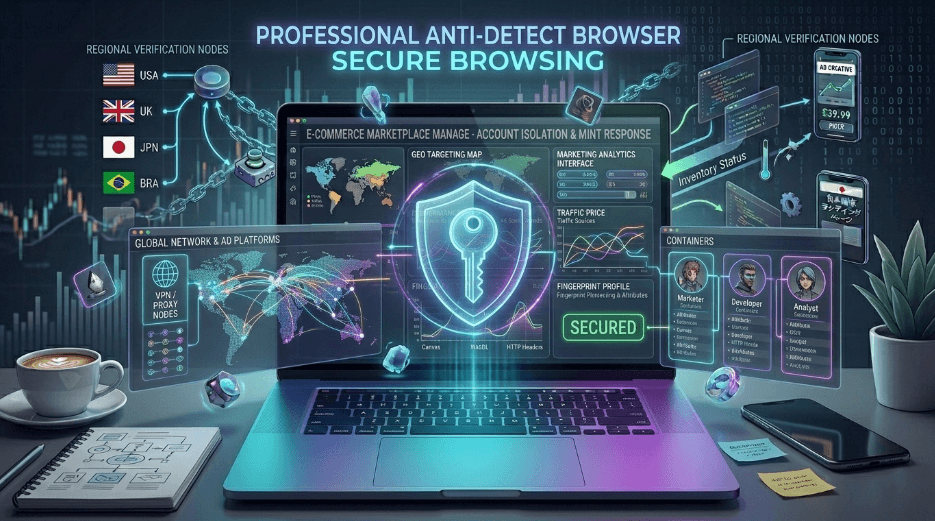
This is precisely why an anti-detect browser has transitioned from a niche utility to an essential professional tool. Unlike standard web browsers, an anti-detect browser is specifically engineered to create completely isolated browsing environments. Each environment, or “profile,” functions as a standalone digital identity with its own unique set of parameters.
Instead of presenting a single, traceable fingerprint to the world, you can manage dozens or even hundreds of distinct profiles that appear to websites as entirely different users on independent devices. This technology goes far beyond what a VPN or Incognito mode can offer, as it addresses the core issue of hardware and software fingerprinting.
Key Components of Secure Profile Isolation
To maintain true online privacy and prevent account linking, each profile in an anti-detect browser can be customized with specific attributes, including:
- Unique Browser Fingerprints: Each session generates a different set of Canvas, WebGL, and AudioContext signals to mimic various hardware configurations.
- Isolated Storage: Every profile maintains its own separate cookies, cache, and local storage, ensuring no data leakage between accounts.
- Network Customization: Users can assign unique proxies or IP addresses to each profile, making them appear to be connecting from different geographical locations.
- System Metadata: You can adjust time zones, languages, screen resolutions, and even hardware-level parameters like CPU cores or RAM to enhance the realism of each identity.
Empowering Professional Workflows
This level of control makes anti-detect browser technology invaluable across various industries. Digital marketers rely on them to manage multiple advertising accounts across platforms like Facebook or Google without triggering automated flags. Developers and QA engineers use them to test how websites perform across different device configurations and regions without needing a physical lab of hardware.
Furthermore, researchers and journalists use these tools to maintain a high degree of online privacy while investigating sensitive topics or studying how tracking algorithms behave in real-time. By controlling the signals exposed through WebGL or HTTP headers, professionals can ensure their secure browsing habits remain undetected by aggressive scripts.
See also: The Future of Technology: 10 Groundbreaking Trends to Watch in 2025
Conclusion: Navigating the Modern Web Safely
As tracking technologies become more sophisticated, the tools we use to protect our identities must evolve accordingly. An anti-detect browser provides the necessary layer of defense against modern fingerprinting techniques that traditional solutions simply cannot block.
When used responsibly for privacy protection, research, or legitimate multi-account management, these tools provide a level of security that is becoming mandatory for anyone operating seriously in the digital space. Understanding and mastering these identities is no longer optional; it is a fundamental skill for maintaining online privacy and ensuring a secure browsing experience in an era of total digital surveillance.